Authenticate to H2O Managed Cloud using AAD
This tutorial guides you through the process of configuring your Azure Active Directory (AAD) as an identity provider (IdP) for your H2O Managed Cloud environment. This enables your users to log in to H2O Managed Cloud through AAD.
Create a new application
The following steps describe how to create a new application in AAD.
-
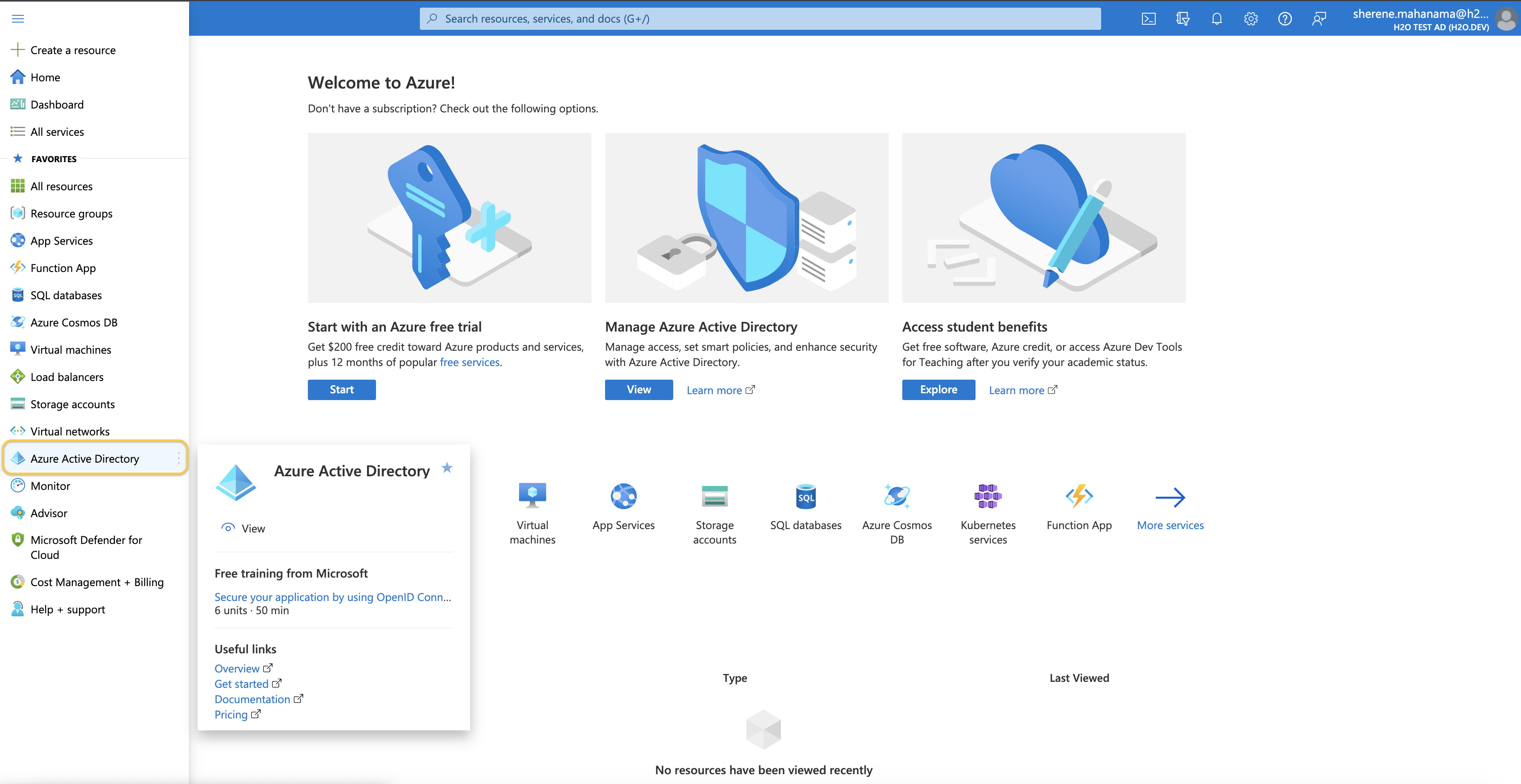
Log in to your Azure portal and navigate to Azure Active Directory.
-
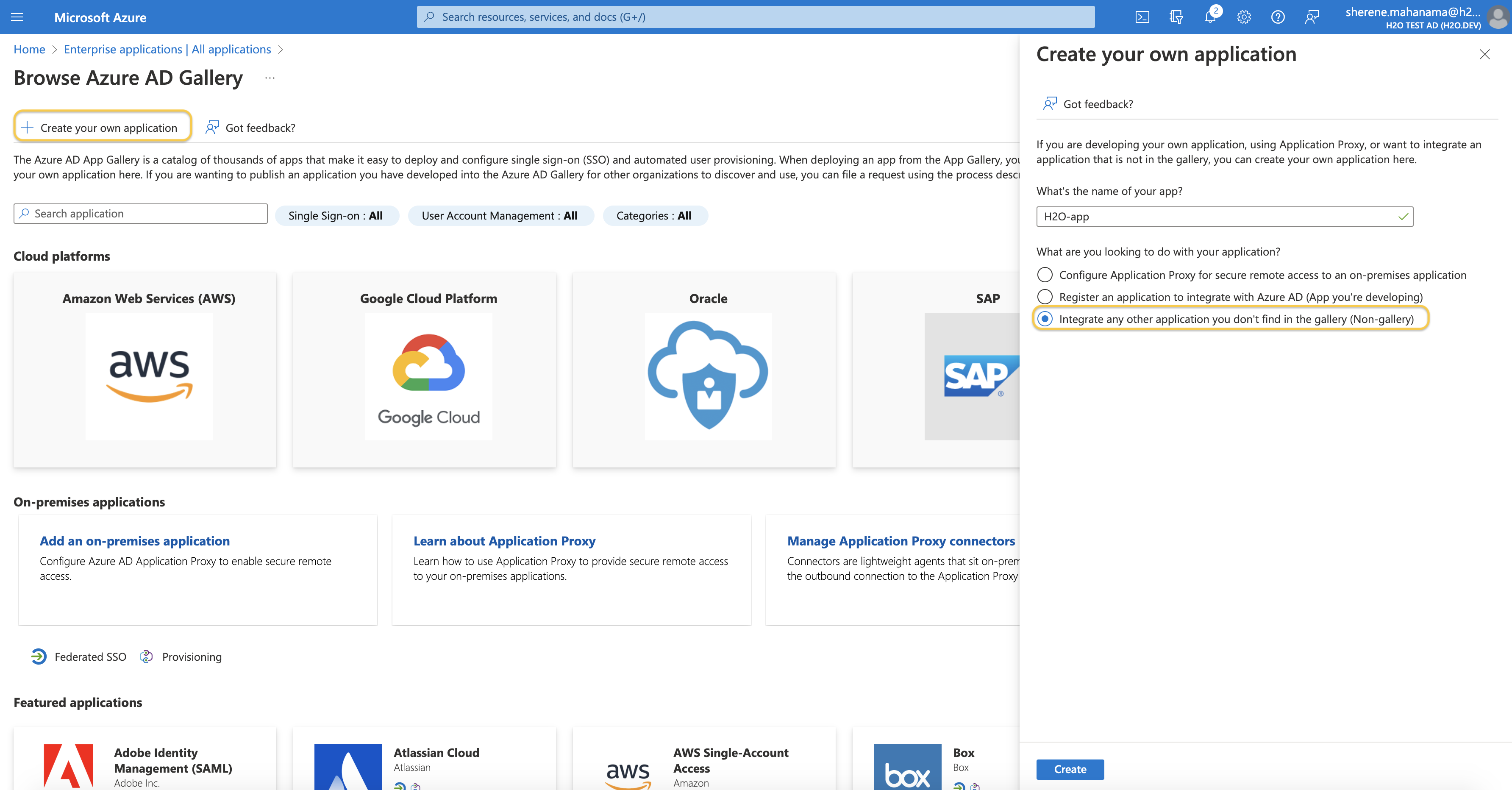
Navigate to Enterprise Applications and then click + New Application.
-
Select Create your own application and name your new application.
-
Select Integrate any other application you don't find in the gallery (Non-gallery) and click Create.
Configure SAML authentication
The following steps describe how to configure Security Assertion Markup Language (SAML) authentication for your AAD application.
-
Click Set up single sign-on and select SAML.
-
Click Edit under Basic SAML Configurations.
-
Enter temporary placeholder values for Identifier (Entity ID) and Reply URL (Assertion Consumer Service URL) - for example,
https://temp.h2o.ai. You will be updating these values later on.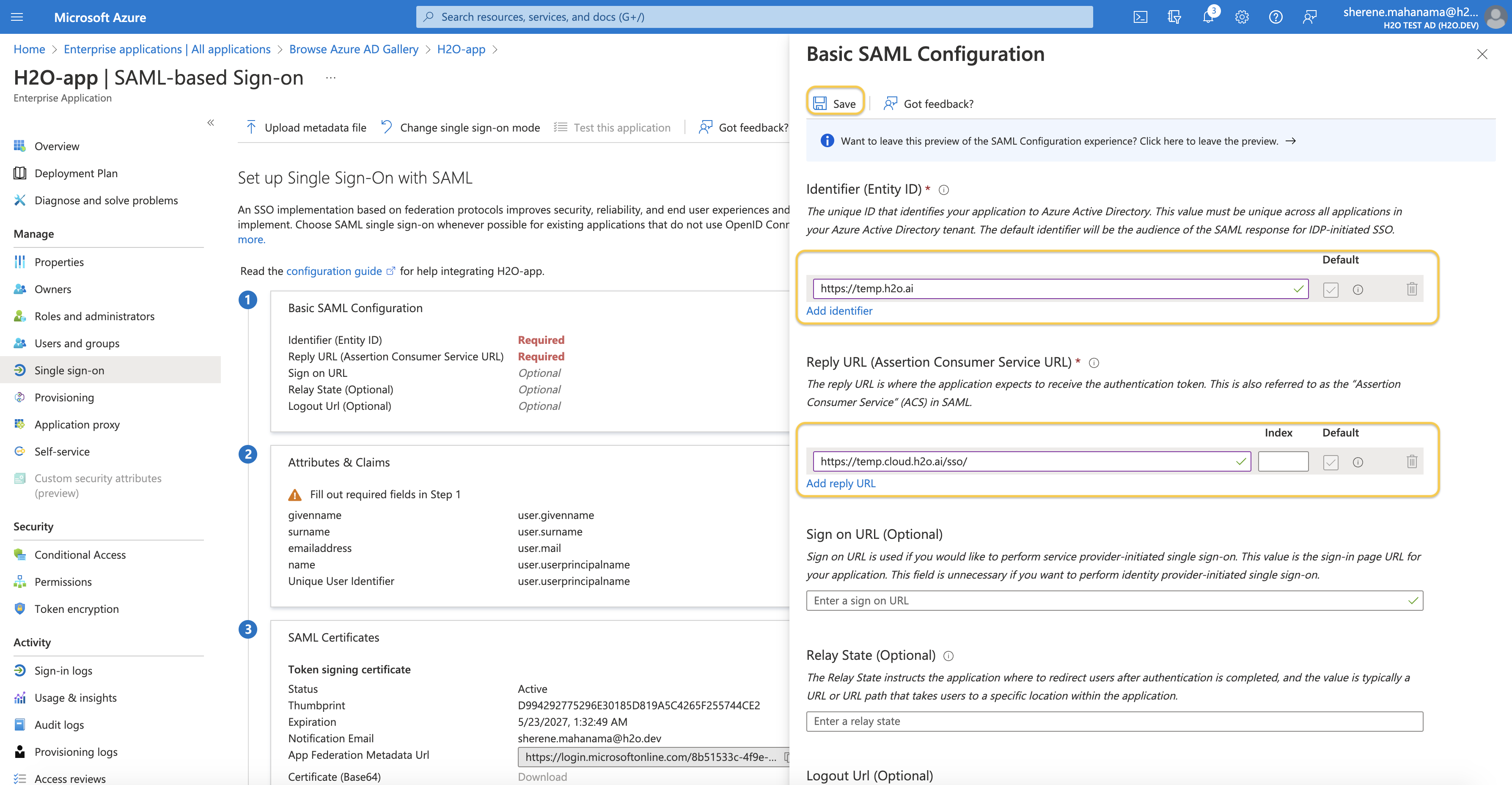
-
Click Save to save your configurations.
-
Under Attributes & Claims, make sure you have the following claims configured.
Claim name Value email user.mail firstName user.givenname lastName user.surname -
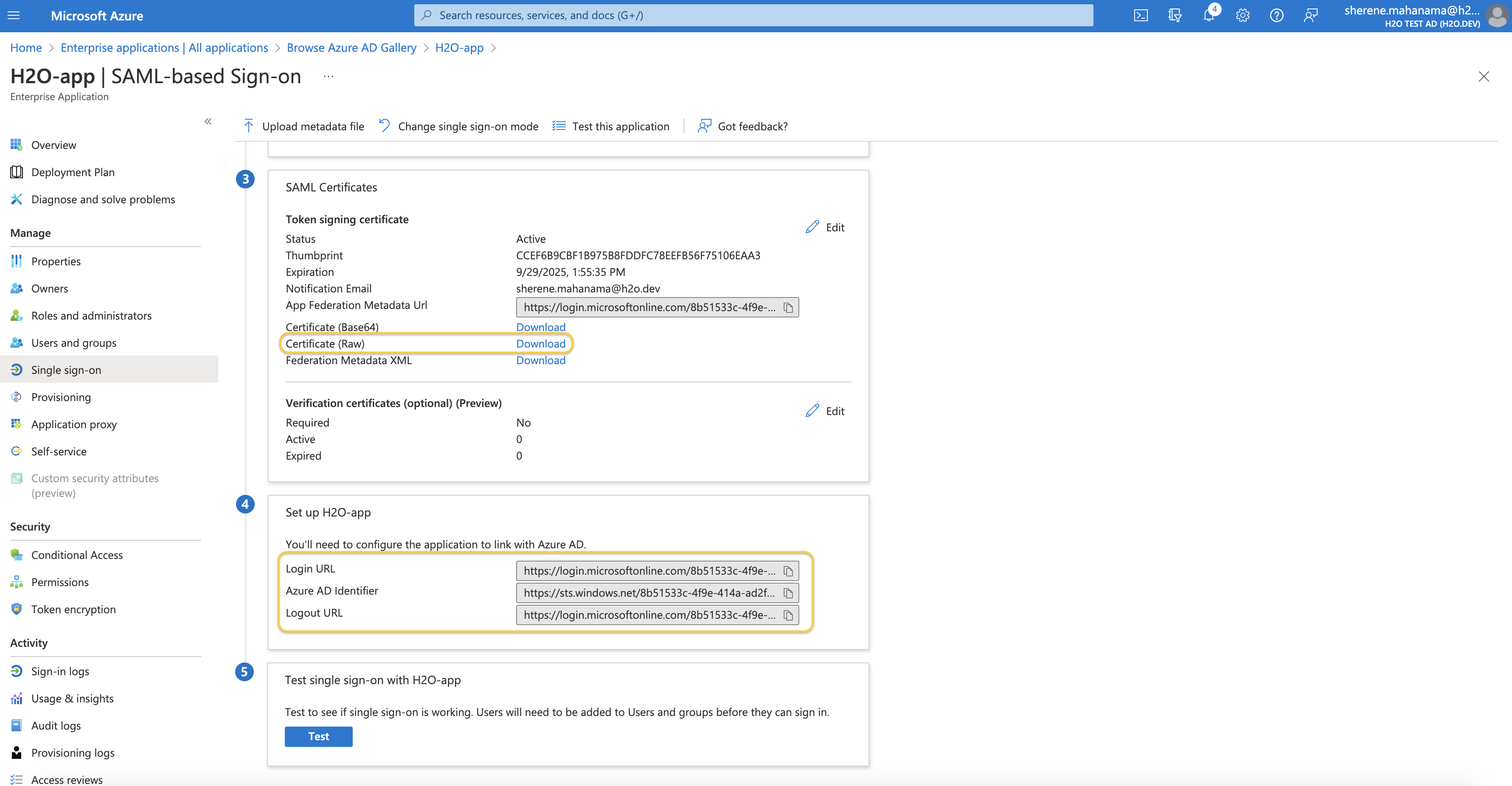
Download the Certificate (Base64) found under the SAML Certificates section.
-
Copy and note down the values for Login URL and Azure AD Identifier found under the Set up [application] section.
Configure your AAD with H2O Managed Cloud
-
Reach out to your H2O representative and request to integrate your AAD with H2O Managed Cloud.
-
Send your H2O representative the Certificate (Base64) that you downloaded earlier, the values for Login URL and Azure AD Identifier from the last step of the section above, and the domain that will be redirected to this IdP.
-
You will receive from H2O an Identifier (Entity ID) and Reply URL (Assertion Consumer Service URL). Navigate back to the Basic SAML Configurations section of your AAD application and replace the temporary placeholders you created earlier in this guide under the Basic SAML Configuration section.
Once fully configured, you will now be able to connect to H2O Managed Cloud using your identity from AAD.
-
If you have existing provisioned users, they will continue working without disruption. On their first login, after the AAD configuration has been completed, they will be automatically sourced from your AAD IdP.
-
Any new user that accesses the newly created AAD enterprise application is automatically connected to the user group of your managed cloud environment.
-
Permission management is still done using the Managed Cloud Admin Center.
-
When working with your AAD as an external IdP, it is the customers' responsibility to make sure identities are fully secure and configured with an MFA (multi-factor authentication).
-
All users that are part of the domain sent to H2O will be re-directed to use the newly created IdP. They will no longer be able to connect using the local Okta password.
- Submit and view feedback for this page
- Send feedback about H2O AI Cloud | Docs to cloud-feedback@h2o.ai